Articles, Interesting Info
HOW TO KEEP HACKERS FROM BREAKING INTO YOUR SECURITY CAMERAS
HOW TO KEEP HACKERS FROM BREAKING INTO YOUR SECURITY CAMERAS
It should come as no surprise that hackers and bots are attacking internet-connected gadgets in this day and age. The recorder or cameras must have an internet connection in order for consumers to remotely watch their security cameras. However, this makes security cameras and systems susceptible to possible intrusions. Fortunately, there are many steps that businesses and homeowners can take to guard against tampered security cameras.
1. Use Strong Passwords and Enable Two-Factor Authentication
Because password security is so crucial, students in primary schools are taught about it. The first line of defense for preventing unauthorized access to computers and Internet of Things (IoT) devices is often passwords. We advise creating distinct, secure passwords for each of your devices. A reliable software-based password manager may help keep passwords safe and guard against their being lost or forgotten. Passwords shouldn’t be shared with someone you don’t trust or who may divulge them to others. Password security may be improved by changing them at least every 90 to 180 days.
Don’t forget to use strong passwords to safeguard your email and social media accounts. Often, it is the recovery email account that is taken first and not the password for the security camera or system that triggers a breach. Visit the website Have I Been Pwned to see if your email address or password has already been compromised and is being circulated online.
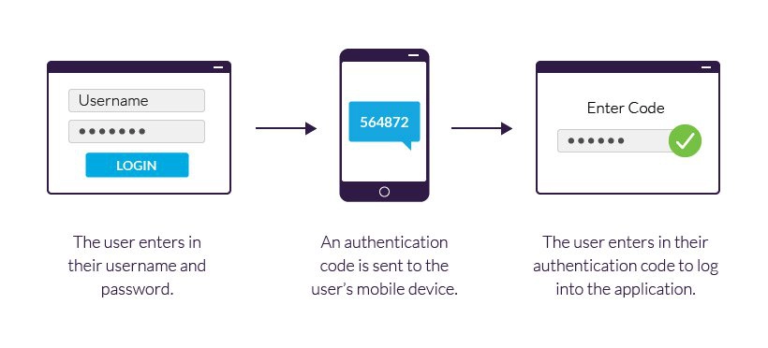
Two-factor authentication is a second line of defense for password security. In order for a login to be permitted, two-factor authentication uses a different device, often a smartphone or an authenticator app. If you log into your bank account online and get a security code through SMS, you may already be familiar with two-factor authentication. For an additional layer of protection, enable two-factor authentication on your email and any other device that supports it.
2. Keep Software and Firmware Updated
Updates to the software or firmware for your security cameras or security system should always be confirmed with the manufacturer or vendor from where you acquired them. Updates might include patches for serious flaws or hacker-usable exploits. Some devices have the ability to scan the internet for updates and download them automatically.
Hackers often exploit outdated software with known vulnerabilities, so ensuring that all security devices are up to date is a critical step in learning how to keep hackers from breaking into your security cameras.
3. Strengthen Your Network Security
The gateway for security cameras and recorders is the local computer network and internet connection. It is simpler for hackers to target cameras and other IoT devices within a network if it has been infiltrated and is readily accessible to hackers.
A smart place to start is by managing your own network with a reliable firewall and having an IT expert examine your network. One of the first things you should do is make sure your router’s firewall is active and put up stringent settings. Denying access to websites from foreign IP addresses is a good general practice. For instance, prohibit IP address ranges coming from countries known for attacking security cameras and systems, such as Russia and China.
4. Purchase Security Cameras from Reliable Sources
The issue is comparable to hazardous counterfeit products available on online marketplaces. Manufacturing efficiency improvements come at the expense of the consumer. Many camera brands are offered at such low rates, but they often lack the necessary research and development to protect them against internet-based assaults.
Poorly developed software can leave security cameras vulnerable to exploitation by hackers. Additionally, there are websites that list hacked security cameras from all around the globe. Some of the more sinister websites provide login credentials for cameras that have been compromised or broadcast footage from compromised cameras for public viewing.
To ensure you are purchasing from a trusted source, buy from IROYAL Security Cameras, which provides reliable and industry-standard surveillance solutions.
Final Thoughts: How to Keep Hackers from Breaking into Your Security Cameras
Now that you know how to keep hackers from breaking into your security cameras, you can take proactive steps to secure your surveillance system. By using strong passwords, enabling two-factor authentication, keeping software updated, strengthening network security, and purchasing from reliable brands, you can significantly reduce the risk of cyber threats.
Ready to upgrade your security? Visit IROYAL Security Cameras today to find the perfect CCTV system for your needs!
Why Choose IROYAL for Your Security Needs?
At IROYAL Security Cameras, we offer:
✅ Reliable security solutions with 24/7 monitoring ✅ High-definition cameras with advanced encryption ✅ Trusted brands like Hikvision, Dahua, EZVIZ, and TP-Link ✅ Expert support for installation and maintenance
Explore Our CCTV Packages Today!
WHY CHOOSE IROYAL?
Checkout what our satisfied customers have been saying about us here!